OWASP Top 10 Pentesting with Penti: Identification and Authentication Failures
Authentication issues are one of the most exploited paths into modern applications. This is due to the fact that attackers can bypass controls by exploiting subtle flaws, even if they appear secure on the surface. Penti tests Identification and Authentication Failures through proof‑based simulated attacks that expose weaknesses in login flows, credential handling, and session behavior before they lead to account compromise or data loss.
Identification and Authentication Failures: overview
Why Test Identification and Authentication Failures with Penti
Authentication weaknesses are rarely obvious. Login systems may function as expected for legitimate users while silently allowing attacker manipulation. Penti pinpoints these failures by actively simulating how adversaries target authentication systems at scale.
Realistic Threat Escalation in a Secure Environment
Targeted Pentesting that Brings Security Assurance
Continuous Validation as Identity Logic Changes
Constant Visibility Through an Intuitive Security Dashboard
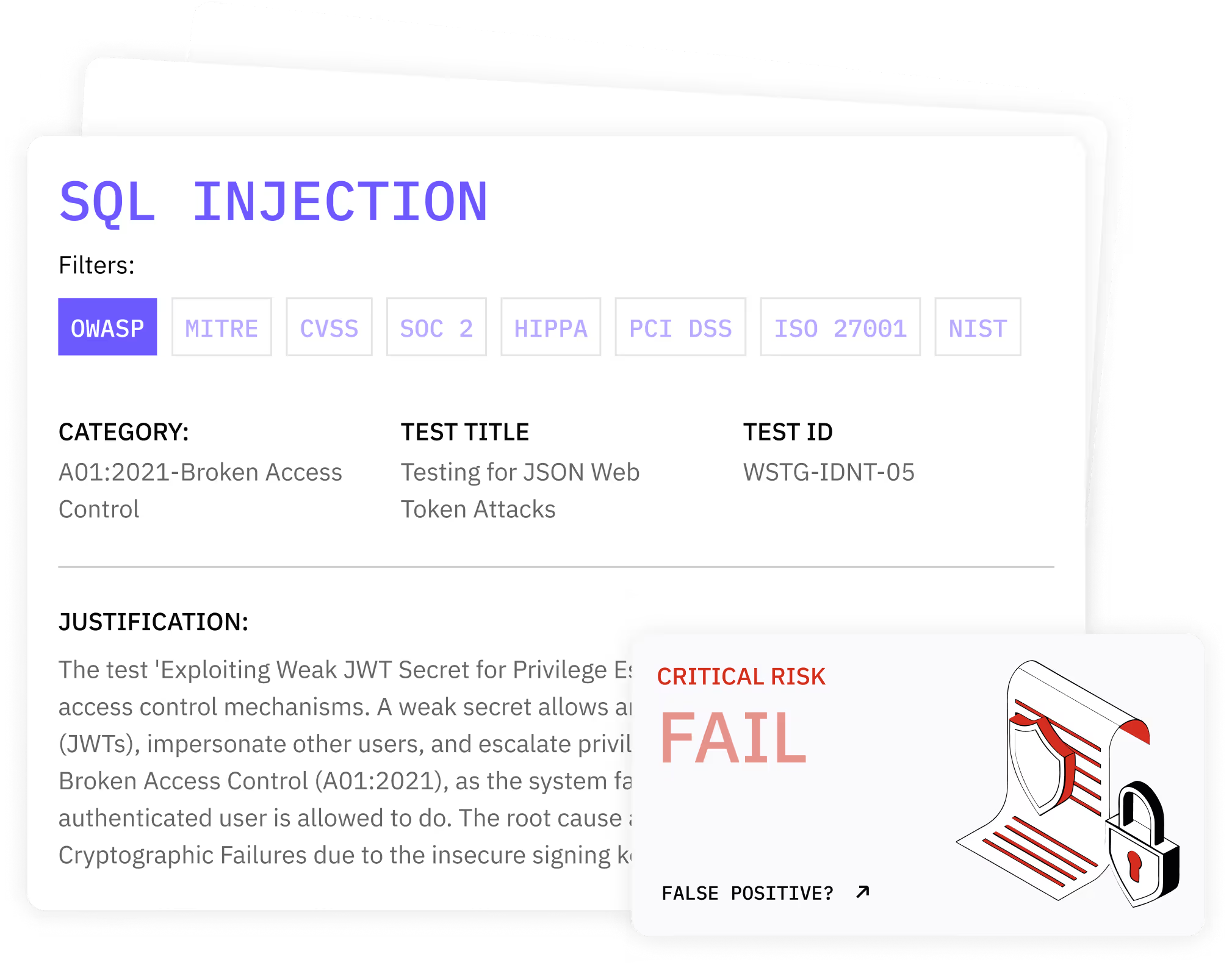
How Penti Detects and Validates Identification and Authentication Failures
Once potential weaknesses are found, Penti simulates realistic attacks using controlled techniques that reflect modern adversary behavior. These tests examine how failures allow attackers to gain unauthorized access or maintain persistence without triggering defenses. Every finding is confirmed through evidence gathered during testing.
Certified human pentesters review and contextualize all results, ensuring identified issues reflect true application behavior rather than outlier cases or noise created by automation alone.
Key features
- Testing for brute force attacks and rate‑limit bypass conditions
- Detection of credential stuffing risk using realistic attack patterns
- Analysis of authentication mechanisms and access enforcement
- Evaluation of session tokens and exposure to session fixation
- Validation of session hijacking attacks under real conditions
- Inspection of session identifiers throughout authenticated flows
What clients receive
- A verified list of exploitable authentication flaws with reproduction steps
- Evidence showing how attackers can gain access or persist
- Business‑focused risk summaries for security leaders
- Developer‑ready remediation guidance and retest recommendations
How Penti Helps You Fix and Reduce Authentication Risks
Teams also receive insight into structural issues such as weak password policies, unsafe credential handling, or ineffective credential recovery paths. This supports long‑term improvement instead of point‑in‑time fixes. By validating fixes through continuous testing, Penti ensures authentication risk stays low as features evolve.
.svg)
.svg)
.svg)
.avif)

Trusted by Teams Protecting Real Users
Security leaders choose Penti to uncover hidden authentication weaknesses before attackers exploit them. Our customers consistently highlight the clarity of proof we provide, along with the relevance of findings, and the speed at which their teams can move from discovery to remediation because of Penti’s expert-led approach.
FAQ
What are Identification and Authentication Failures?
Identification and Authentication Failures are security vulnerabilities where systems fail to correctly verify users or protect authenticated sessions. These failures allow attackers to bypass controls or assume another user’s privileges.
Why are authentication issues so common?
Authentication flows are complex and often evolve over time. As features are added, assumptions break and gaps appear. Automated attacks can exploit these weaknesses faster than teams can discover them manually.
How do attackers abuse login systems?
Attackers use techniques such as automated scripts to test username password combinations at scale. When protections are weak, they can exploit failed login attempts to compromise accounts without raising alarms.
Does this testing cover passwords and credential storage?
Yes. Penti evaluates how applications handle storing passwords, checks for insecure password storage practices, and identifies exposure caused by weak hashing algorithms or default credentials.
How does Penti test session security?
Penti examines how authenticated session state is created, maintained, and terminated. This includes detecting poor session management that could enable hijacking or persistence beyond logout.
How often should authentication testing be performed?
Authentication testing should run continuously. Login paths change frequently as features evolve, and users reuse passwords in ways that increase risk over time.














