OWASP Top 10 Pentesting with Penti: Insecure Design
Penti finds AppSec weakness at the design stage before your code ships. Our agents test the intent of features and verify guardrails in real flows. Your security team gets clear evidence of broken or missing security controls. Our guidance maps gaps to secure design principles so teams fix root causes fast.
Insecure Design: Overview
Test for Design Weaknesses with Penti’s Agentic AI
Design‑level issues are hard to catch and expensive to fix after launch. Penti helps teams identify and resolve these gaps early by validating how features are meant to work and how they can be abused in practice. Our Agentic AI delivers repeatable evidence, clear ownership, and guidance that leads to durable fixes.
Test feature intent, not just code
Align security testing with how you build
Get developer‑ready evidence and guidance
.svg)
Prioritize risk with business context
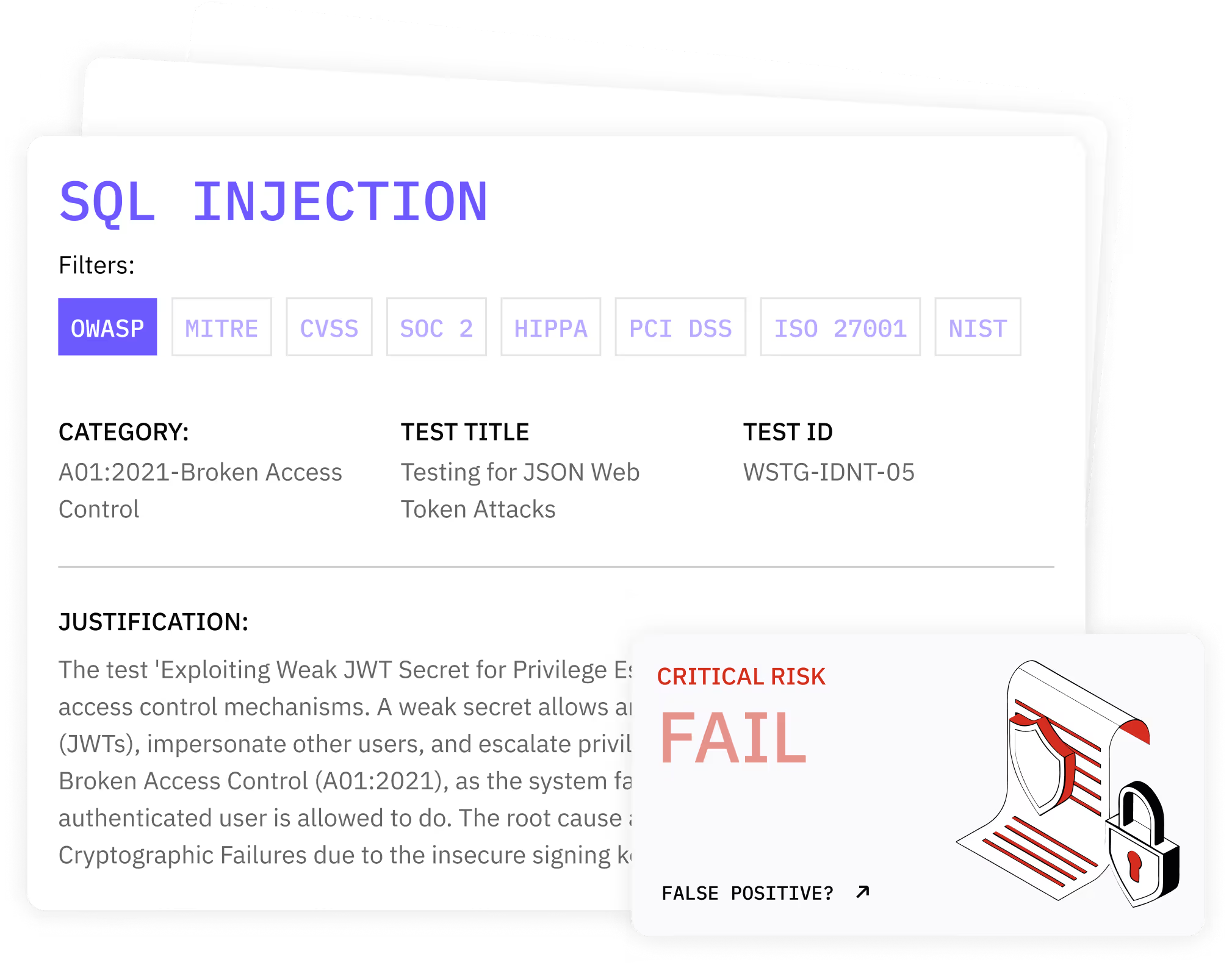
How Penti detects and validates design weaknesses
Key features
- Abuse‑case exploration across potential attack vectors in live environments
- Logic‑aware attack simulation for injection attacks, cross site scripting, and sql injection where design choices expose these paths
- Resilience checks against brute force attacks and ddos attacks that target workflow bottlenecks
- Session and identity hardening to prevent account takeover
- Behavioral probes that surface misuse of workflows that do not involve malicious code
What clients receive
- A verified list of potential vulnerabilities with reproduction steps and impact evidence
- Clear mapping to affected assets and sensitive data exposure
- Design fixes and control placement guidance for developers
- Audit‑ready reports with risk context and recommended retest schedules
How Penti helps you fix and reduce risk
.svg)
.svg)
.svg)
.avif)

Trusted by product and security leaders
Teams use Penti to validate critical flows before release, valuing the clear proof and unlimited retests Penti provides. Penti ties evidence to business impact and ownership, creating shared priorities and significant risk reduction across the company.
FAQ
What is an insecure design?
Insecure Design is a broad vulnerability class, consisting of security errors and oversights in software services and web applications. The result is a path that an attacker can abuse without breaking code.
How can insecure design be prevented?
Companies can prevent insecure design by starting with clear abuse‑case thinking, and continuing with the addition of secure controls at every trust boundary. It’s important to validate behavior in staging and production and align controls to design patterns that prevent exploitation.
What is the primary concern with insecure design?
Insecure Design allows attackers to use normal features in harmful ways. The risk often appears without exploits but through logic that allows privilege jumps, resource abuse, or quiet data exposure.
How does Penti test for insecure design?
Our autonomous agents follow real user paths, testing state, authorization, and workflow decisions, checking access control and input validation across key steps, verifying rate limit and privilege transitions, then link each finding to fixes that your team can ship.
What kinds of impact can result from insecure design?
Impact can range from fraud to total outages. You may see security breaches, lost revenue, or abuse of resources. You may also see quiet leaks from unprotected storage. Small gaps can enable privilege growth or fraud at scale.
How is this different from code‑level testing?
Code tests look for defects in functions or libraries, whereas design tests look for misuse of workflows and trust. Design tests pinpoint policy gaps, missing controls, and weak process gates.














