OWASP Top 10 pentesting with Penti: Server-Side Request Forgery (SSRF)
Penti’s OWASP top 10 penetration testing process uses AI-driven reconnaissance, attack simulation, and real-time validation to uncover vulnerabilities that can be exploited by server-side request forgery (SSRF). Penti’s testing for SSRF examines web applications and rapidly generates reports with actionable remediation guidance.
SSRF: Overview
Uncover Critical Weaknesses before SSRF Attacks Do
Penti is more than an SSRF testing tool, it’s a versatile security solution powered by a combination of agentic artificial intelligence and the expertise of human cybersecurity experts. Our curated threat intelligence ensures that your application remains secure while probing for improper input validation and ineffective access controls.
Rapid and realistic testing across applications
Vulnerability detection that goes further
Pentesting that scales with you
Streamlined compliance and reduced risk

How Penti Exposes SSRF Risks
Key features
- Penti identifies weak points in how your application handles URLs and processes user input, helping you spot areas where attackers could misuse the system.
- Penti’s platform uncovers hidden or “blind” SSRF issues by monitoring how the application behaves when it receives unusual requests, even when no direct response is shown.
- Penti’s agents test a wide range of real‑world techniques used by attackers to slip past weak filters, ensuring your defenses hold up under pressure.
- Our security experts review the results and confirm whether your protections, such as allow‑lists or traffic‑filtering rules, are working as intended.
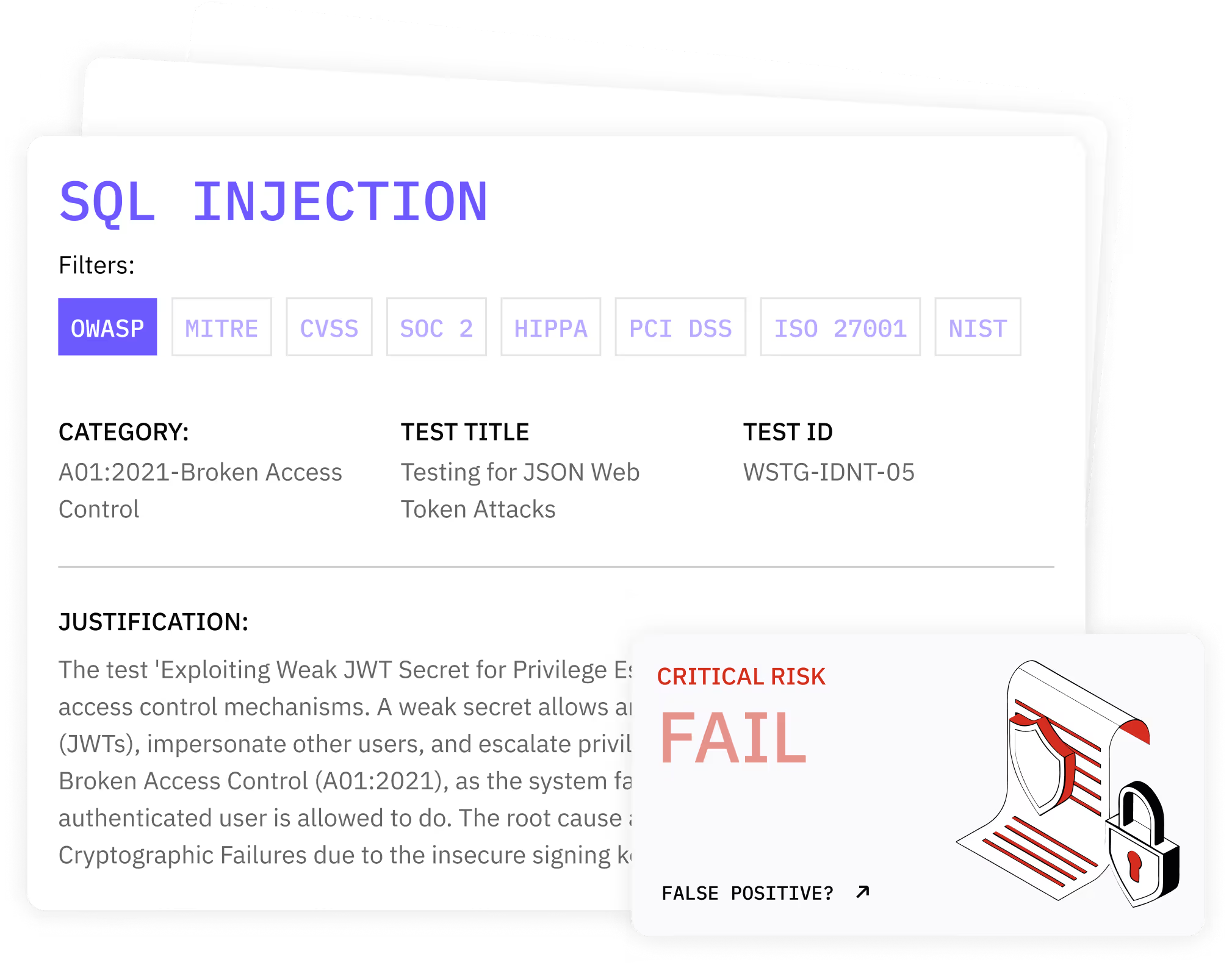
What clients receive
- A verified list of exploitable SSRF vulnerability points
- An executive risk summary and developer remediation playbook.
- Evidence artifacts for audits and a recommended retest schedule using our SSRF test site capabilities.
How Penti Helps You Prevent SSRF Attacks
.svg)
.svg)
.svg)
.svg)
.avif)

What our clients say
Security teams across SaaS, fintech, and enterprise software trust Penti to uncover SSRF weaknesses early, reduce breach risk, and strengthen their application security posture.
Related OWASP Pentesting Checks
Discover additional OWASP Top 10 vulnerabilities that attackers frequently combine with SSRF to access internal systems, manipulate services, or expose sensitive data.
SQL Injection
Security Misconfiguration
Broken Access Control
Cryptographic Failures
Insecure Design
Identification and Authentication Failures

Software and Data Integrity Failures
Vulnerable and Outdated Components
FAQ
What is the difference between CSRF and SSRF?
SSRF manipulates a server into making unauthorized requests to internal or external systems, whereas CSRF forces a user’s browser to perform unwanted actions. In short, SSRF targets servers, and CSRF targets users.
How does Penti detect SSRF vulnerabilities?
Penti analyzes URL‑handling logic, tests request‑routing behavior, probes internal services, and uses out‑of‑band detection to uncover blind SSRF.
Can SSRF lead to data breaches?
Yes. SSRF can expose internal resources, cloud metadata, system files, and sensitive data, enabling attackers to escalate access or exfiltrate information.
Does Penti test for cloud‑specific SSRF risks?
Absolutely. Penti checks for access to cloud metadata endpoints such as AWS, GCP, and Azure, which are common SSRF targets.
How long does an SSRF pentest take?
Most assessments complete within 24–72 hours, depending on application size and complexity.
Will Penti’s testing disrupt my application?
No. Penti uses safe, controlled testing methods designed to avoid impacting production.
Does Penti provide remediation guidance?
Yes. You receive developer‑ready instructions, validation steps, and a retest schedule to ensure fixes are effective.














