OWASP Top 10 pentesting with Penti: Security Misconfiguration
Don’t let security misconfigurations expose sensitive data and expand your attack surface. Launch Penti and gain real-time insight into security gaps that can lead to breaches. Penti’s agentic AI delivers end‑to‑end security misconfiguration testing that discovers, validates, and prioritizes misconfigs with clear fixes, so your team can harden systems fast and sustain secure defaults.
Security Misconfiguration: overview
Why Test for Security Misconfigurations with Penti’s Agentic AI
Penti combines autonomous AI agents and human expertise to systematically identify security misconfigurations, validate exploitability, and recommend precise, developer-ready remediation paths. Unlike most automated scanners, Penti maps your entire ecosystem, including web applications, APIs, infrastructure, and cloud services, to uncover hidden misconfiguration chains and security flaws that can surface from weak security controls or insecure default settings.
AI-enabled scope and speed
Validation-first security reporting

Practical guidance on fixes and remediation
Unlimited targeted retesting

How Penti Detects & Validates Security Misconfiguration Vulnerabilities
Key features
- Automated discovery of weak or missing security headers, exposed directory listing, and unsafe debug modes.
- Cloud misconfiguration checks that review cloud storage permissions, IAM policies, and overly permissive resource access.
- Detection of default configurations, default credentials, outdated services, and insecure admin interfaces.
- Drift analysis across environments to identify configuration drift and highlight deviations from secure defaults.
- Validation of firewall rules, network devices, and platform hardening (e.g., disabled/no unnecessary features).
- Verification of your patch management process to ensure systems apply security patches and maintain current component versions.
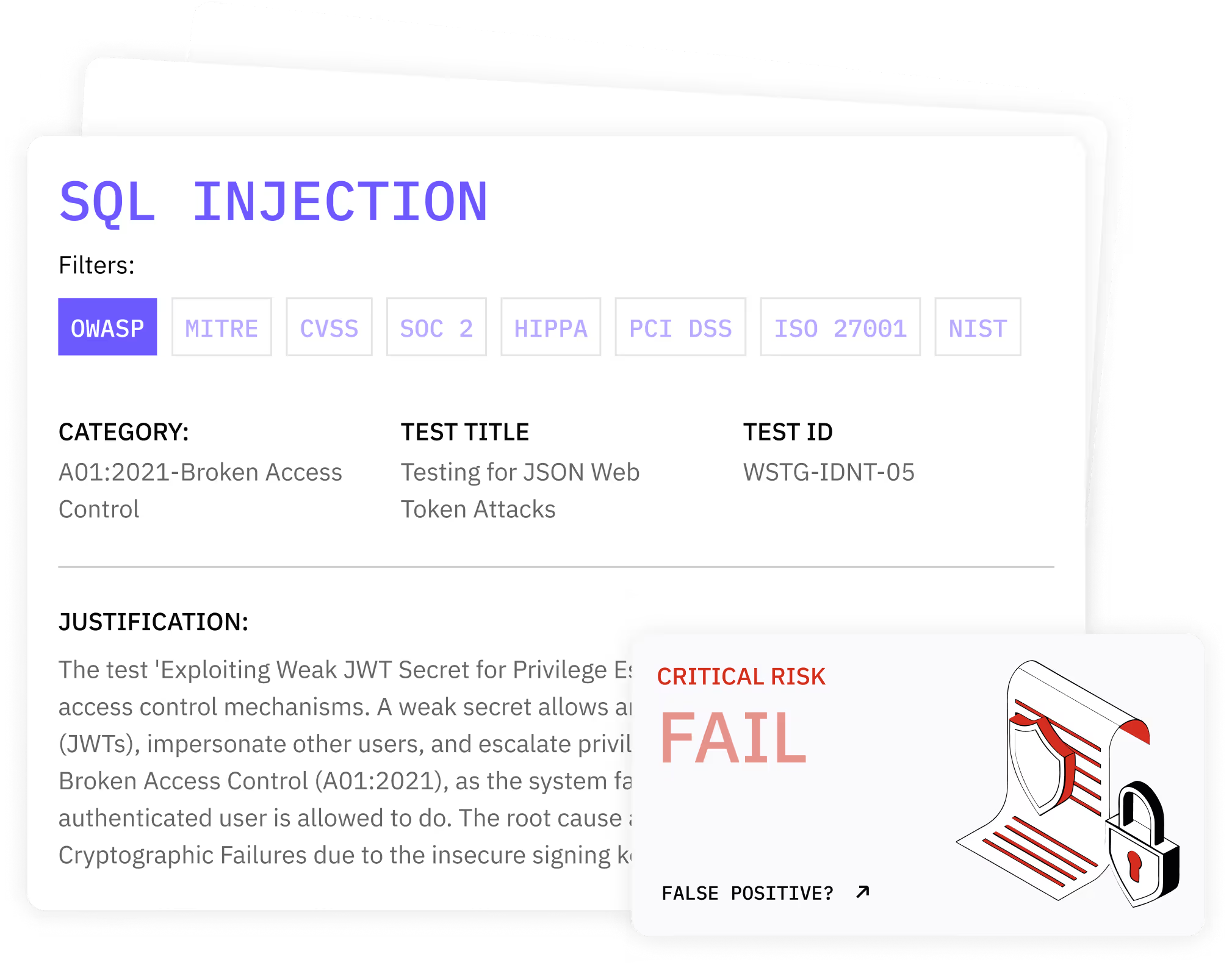
What clients receive
- A validated list of misconfigurations with full reproduction steps, impact summaries, and evidence artifacts.
- A prioritized remediation plan with configuration hardening guidance and environment-specific fix instructions.
- Executive reporting that supports compliance, audit readiness, and stakeholder communication.
- Recommended retesting schedules and continuous monitoring to prevent regressions and catch new drift early.
How Penti Helps You Fix and Reduce Risk
.svg)
.svg)
.svg)
.avif)

Trusted by Teams Who Prioritize Real Security
For security leaders in need of rapid security assurance, Penti offers validated results and clear remediation. Teams of all sizes employ our platform to reduce misconfig-related incidents and boost compliance.
FAQ
What is an example of a security misconfiguration?
Security misconfigurations can include leaving default passwords enabled, exposing directory listing, missing security headers, overly permissive cloud storage buckets, or verbose error pages that leak environment details and configuration files.
How can security misconfigurations cause breaches?
Weak or incorrect security configuration can let adversaries gain unauthorized access, move laterally, and expose sensitive data. Even a single misconfigured rule can allow data exfiltration, privilege escalation, or service disruption, culminating in regulatory fines and brand damage.
How does Penti validate findings and reduce false positives?
Penti safely simulates attacker behavior to confirm exploitability, then links each issue to actual impact (e.g., data disclosure or privilege overreach). Your team gets reproducible proofs, prioritized risk, and remediation steps to resolve the issue quickly.
Can Penti help with on-prem and cloud?
Yes. Penti evaluates web servers, application server configurations, network security controls, and major cloud providers. It also checks policies, identities, and storage settings to restrict access and disable unnecessary features.
How do companies prevent misconfigurations?
Adopt hardened baselines and secure defaults, enforce IaC, automate checks in CI/CD, and maintain an effective patch management process to apply security patches rapidly. Continuous testing helps catch configuration drift before it can spiral out of control.














